Advanced SAML configuration
What will you learn in this topic?
By the end of this topic, you will be able to understand:
- How to enable encrypted SAML assertions.
- How to use Harness local login as a fallback.
- How to configure the default landing page experience for your users.
Before you begin
- A Harness account with Account Admin permissions to modify authentication settings.
- An active SAML SSO provider already configured in Harness
Harness Local Login
To prevent lockouts or in the event of OAuth downtime, a user that has Account Admin assigned on All Account Level Resources or All Resources Including Child Scopes can use the Local login URL https://app.harness.io/auth/#/local-login to sign in and update the OAuth settings.
Harness Local Login signs in to the default account for the user. If the user is assigned to multiple accounts, the user must ensure the default account is set correctly before attempting to use Harness Local Login.
For the Harness production cluster prod-3, the local login URL is https://app3.harness.io/auth/#/local-login.
-
Sign in using Local login.

-
Change the settings to enable users to log in.
You can disable Local login using the feature flag DISABLE_LOCAL_LOGIN. Contact Harness Support to enable the feature flag.
This page covers advanced SAML configuration options in Harness, including local login fallback, encrypted SAML assertions, and setting the default UI experience for your users.
If you use Harness Self-Managed Enterprise Edition, your instance must be accessed via an HTTPS load balancer. SAML authentication will fail over HTTP.
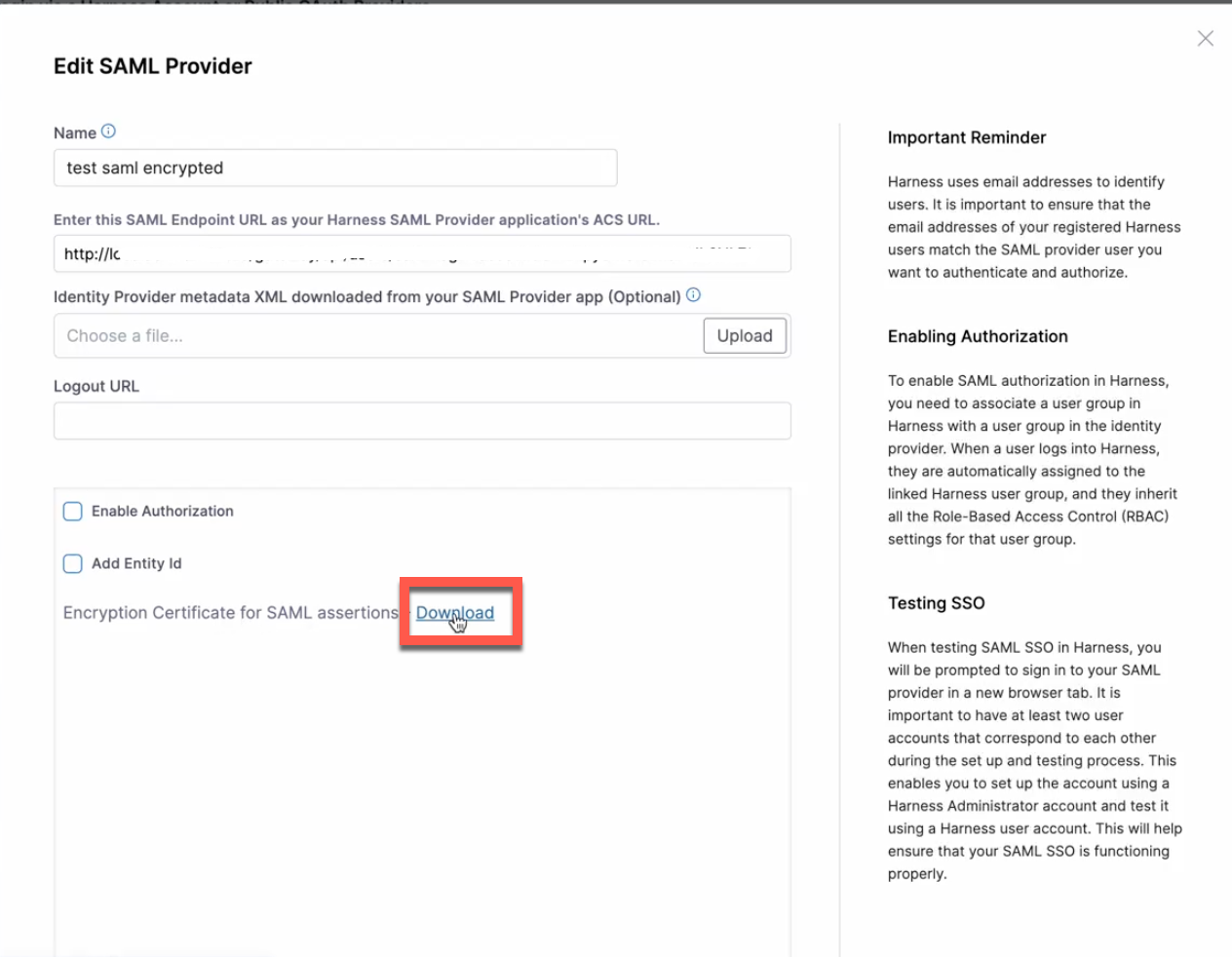
Use encrypted SAML
To use encrypted SAML with Harness, you download the encryption certificate from the Harness UI and upload it to your identity provider (IdP) settings to support the encrypted SAML flow.
To download your encryption certificate and upload it to your IdP settings, do the following:
-
In your Harness account, go to Account Settings, and then select Authentication.
-
Under Login via SAML, select More Options (⋮), and then select Edit. The Edit SAML Provider options open.
-
Select the Download link to download the encryption certificate for SAML assertions.
-
Sign in to your IdP.
-
Edit your SAML integration.
- Enable assertion encryption.
- Select your encryption algorithm.
- Upload the encrypted certificate file you downloaded from the Harness UI in step 3 above.
When you sign in to Harness via SAML, the operation is completed using encrypted assertions.
Set the default experience
Environment administrators can set the default Harness generation landing page, FirstGen or NextGen, for their users to ensure the correct Harness Experience is provided to each user. For more information, go to Account details.