Keycloak
What will you learn in this topic?
By the end of this topic, you will be able to understand:
- How to set up a Keycloak SAML client.
- How to configure Harness to use Keycloak SAML client as an SSO provider.
- How to enable group-based authorization.
Before you begin
- A Harness account with Account Admin permissions.
- An existing Keycloak instance with admin access to create and configure SAML clients.
You can use Keycloak as a SAML identity provider for Harness, letting Keycloak users log in to Harness with their existing credentials and optionally syncing Keycloak group memberships to Harness user groups automatically.
If you use Harness Self-Managed Enterprise Edition , your instance must be accessed via an HTTPS load balancer. SAML authentication will fail over HTTP.
Harness supports configuration with or without Just-In-Time (JIT) user provisioning. Without JIT, perform the following steps to add new users:
- In Harness, add the users you want to set up for SAML SSO by inviting them to Harness using the same email addresses that they use in your SAML provider.
- In Keycloak, add the users and make sure they are in scope for the client you create in the configuration steps below.
With JIT, you add users to Keycloak, and they will automatically be added to Harness upon first login.
Set up a client in Keycloak
-
Log in to your Keycloak account.
-
Switch to your target Realm, then select Clients.
-
Select Create Client, then enter the following values.
General settings
Field Description Client Type SAML Client ID app.harness.io Name optional Description optional Always display in UI Off Login settings
Field Description Root URL https://app.harness.io/Home URL https://app.harness.io/ng/account/<YOUR ACCOUNT ID>/main-dashboardValid post logout redirect URIs https://app.harness.io/ng/account/<YOUR ACCOUNT ID>/main-dashboardMaster SAML Processing URL https://app.harness.io/gateway/api/users/saml-login?accountId=<YOUR ACCOUNT ID>
If the account uses a vanity URL, then use the vanity URL in your SAML setup. For example, https://<yourvanityurl>/gateway/api/users/saml-login?accountId=<YOUR ACCOUNT ID>.
-
Select Save.
-
In the newly-created client's configuration, enter the following values.
Settings -> SAML capabilities
Field Description Name ID format email Force POST binding On Include AuthnStatement On All other options Off Settings -> Signature and Encryption
Field Description Sign documents On Sign assertions On Signature algorithm RSA_SHA256 SAML signature key name NONE Canonicalization method EXCLUSIVE Keys
Field Description Client signature required Off Advanced
Field Description Assertion Consumer Service POST Binding URL https://app.harness.io/gateway/api/users/saml-login?accountId=<YOUR ACCOUNT ID> -
Select Save.
-
From the left-nav menu, go to Realm Settings, then select SAML 2.0 Identity Provider Metadata. A new tab opens with XML data.
-
Save the data to a file to use when configuring Harness.
-
(Optional) To automatically sync group memberships in Harness based on group memberships in Keycloak, perform the following steps.
-
Go to your newly-created Client, then select the Client Scopes tab.
-
In the first row, select the value in the Assigned client scope field.
-
Select Configure a new mapper, then select Group list.
-
Configure the following settings.
Name Description Name grouplist Group attribute name member SAML Attribute NameFormat Basic Single Group Attribute On Full group path Off - Select Save.
-
Set up Keycloak SAML SSO in Harness
-
In your Harness account, go to Account Settings, and then select Authentication.
-
Select + SAML Provider, then enter the following values.
Field Description Name Keycloak Select an SAML Provider Other Enable Authorization Enable if you want to automatically sync group memberships in Harness based on group memberships in Keycloak Group Attribute Name member (only available if Enable Authorization is selected) Add Entity Id Enabled Entity Id app.harness.io Enable JIT Provisioning Enable if Just In Time user provisioning is desired -
Select Add.
-
In Upload the Identity Provider metadata XML downloaded from your app, select Upload, then select the XML file you added when you set your Keycloak configuration steps.
-
Select Add. The new SSO provider is displayed under Login via SAML. You might need to expand this section using the arrow on the right-hand side of the screen.
Enable and test SSO with Keycloak
Now that Keycloak is set up in Harness as a SAML SSO provider, you can enable and test it.
- To enable the SSO provider, select Login via SAML.
- In the resulting Enable SAML Provider dialog, click TEST to verify the SAML connection you've configured.
- Upon a successful test, Harness will display the SAML test successful banner on top.
- Click CONFIRM to enable SAML SSO in Harness.
Harness Local Login
To prevent lockouts or in the event of OAuth downtime, a user that has Account Admin assigned on All Account Level Resources or All Resources Including Child Scopes can use the Local login URL https://app.harness.io/auth/#/local-login to sign in and update the OAuth settings.
Harness Local Login signs in to the default account for the user. If the user is assigned to multiple accounts, the user must ensure the default account is set correctly before attempting to use Harness Local Login.
For the Harness production cluster prod-3, the local login URL is https://app3.harness.io/auth/#/local-login.
-
Sign in using Local login.

-
Change the settings to enable users to log in.
You can disable Local login using the feature flag DISABLE_LOCAL_LOGIN. Contact Harness Support to enable the feature flag.
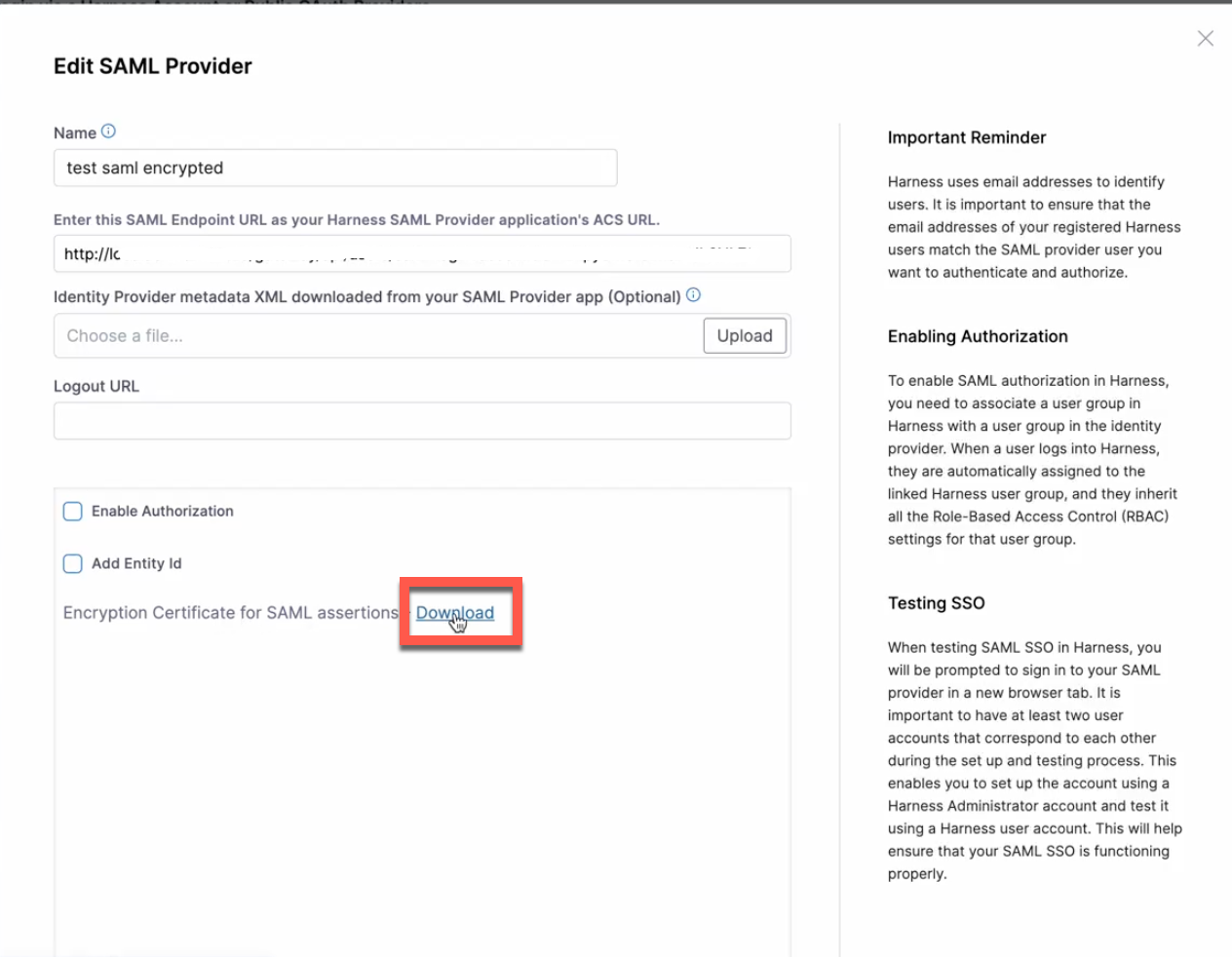
Use encrypted SAML
To use encrypted SAML with Harness, you download the encryption certificate from the Harness UI and upload it to your identity provider (IdP) settings to support the encrypted SAML flow.
To download your encryption certificate and upload it to your IdP settings, do the following:
-
In your Harness account, go to Account Settings, and then select Authentication.
-
Under Login via SAML, select More Options (⋮), and then select Edit. The Edit SAML Provider options open.
-
Select the Download link to download the encryption certificate for SAML assertions.
-
Sign in to your IdP.
-
Edit your SAML integration.
- Enable assertion encryption.
- Select your encryption algorithm.
- Upload the encrypted certificate file you downloaded from the Harness UI in step 3 above.
When you sign in to Harness via SAML, the operation is completed using encrypted assertions.
Set the default experience
Environment administrators can set the default Harness generation landing page, FirstGen or NextGen, for their users to ensure the correct Harness Experience is provided to each user. For more information, go to Account details.