Policy as Code for Services
Harness provides governance using Open Policy Agent (OPA), Policy Management, and Rego policies.
You can create a policy and apply it to all services in your Account, Org, or Project. The policy is evaluated on service-level events:
- On Save — evaluated when a service is created or updated.
- On Run — evaluated when a pipeline that references the service is executed.
For more details, see the Harness Governance Quickstart.
Prerequisites
- Harness Governance Overview
- Harness Governance Quickstart
- Policies use the OPA authoring language Rego. For more information, see OPA Policy Authoring.
Step 1: Add a policy
-
In Harness, go to Account Settings → Policies → New Policy.
-
Enter a Name for your policy and click Apply.
-
Add your Rego policy in the editor.
You can write your own Rego policy or use a sample from the Library panel. Select the Library tab, choose Entity: Service from the dropdown, and pick one of the built-in samples:
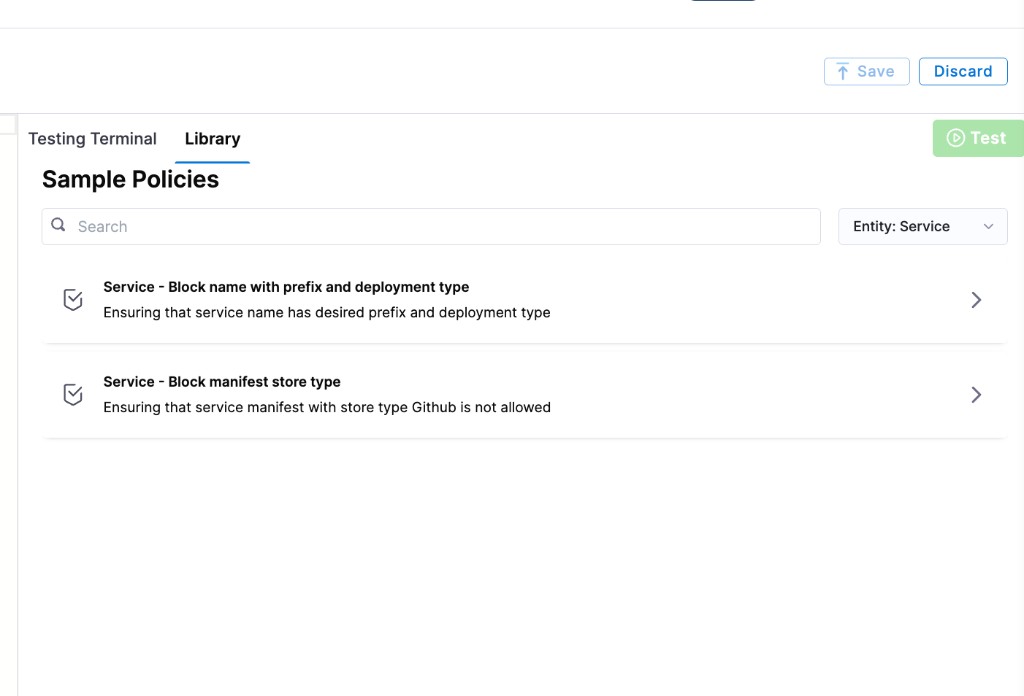
Harness ships two sample policies for services:
- Service – Block name with prefix and deployment type: Ensures a service name contains a required prefix and uses an allowed deployment type.
- Service – Block manifest store type: Prevents services from using a specific manifest store type (for example, GitHub).
Below are example Rego policies you can use as a starting point.
Block services by deployment type or name prefix
package service
deny[msg] {
input.serviceEntity.serviceDefinition.type == "Kubernetes"
msg := "Service with Kubernetes deployment type is not allowed"
}
deny[msg] {
startswith(input.serviceEntity.name, "BLOCKED_SERVICE_NAME")
msg := "Service which starts with BLOCKED_SERVICE_NAME prefix is not allowed"
}
Block services that use a forbidden manifest store type
package service
deny[msg] {
input.serviceEntity.serviceDefinition.spec.manifests[0].manifest.spec.store.type == "Github"
msg := "Service with Github store type is not allowed for manifest"
}
- Click Save.
Step 2: Add the policy to a policy set
After creating your policy, add it to a Policy Set before it can be enforced on services.
-
Go to Policies → Policy Sets → New Policy Set.
-
Enter a Name and optional Description for the Policy Set.
-
In Entity type, select Service.
-
In On what event should the Policy Set be evaluated, select On Save, On Run, or both depending on when you want the policy enforced.
- On Save — the policy is evaluated every time a user creates or updates the service.
- On Run — the policy is evaluated when a pipeline that uses the service is executed.
-
Click Continue.
noteExisting services are not automatically evaluated against new policies. Policies are applied only when a service is saved (created or updated) or when a pipeline referencing the service is run.
-
In Policy evaluation criteria, click Add Policy.
-
In the Select Policy dialog, choose the scope (Project, Org, or Account) and select the policy you created.
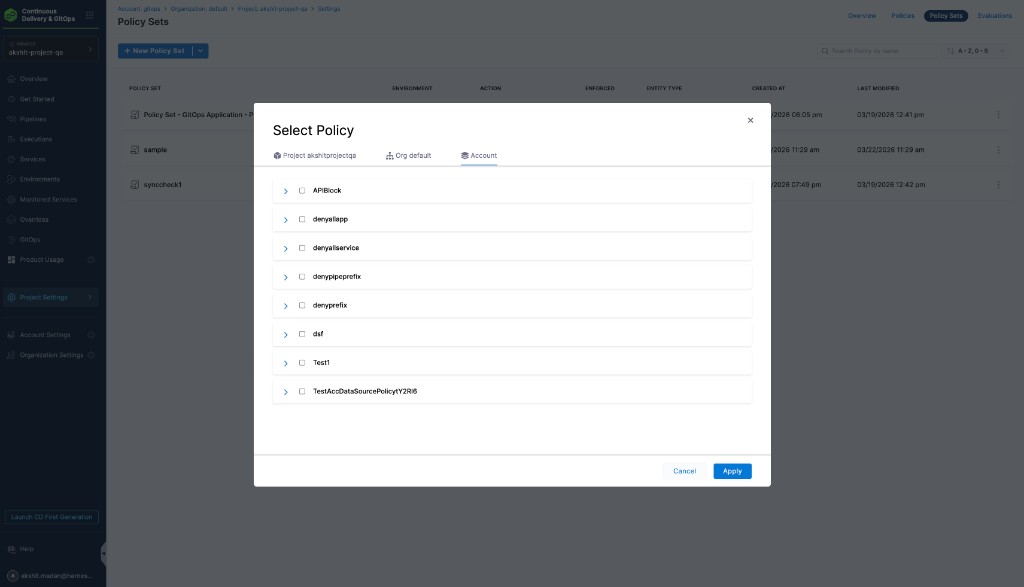
-
Select the severity and action for policy violations:
- Warn & continue — a warning is displayed if the policy is not met, but the service is saved and you can proceed.
- Error and exit — an error is displayed and the service is not saved if the policy is not met.
-
Click Apply, then click Finish.
-
The Policy Set is automatically set to Enforced. To disable enforcement, toggle off the Enforced button.
Step 3: Apply the policy to a service
After creating and enforcing your Policy Set, it is automatically evaluated whenever a service event matches the configured trigger.
-
Go to Deployments → Services → New Service (or edit an existing service).
-
Configure the service and click Save.
-
Based on your selection in the Policy Evaluation criteria:
- If the service meets the policy, it is saved successfully.
- If the service violates the policy and the severity is Warn & continue, it is saved with a warning.
- If the service violates the policy and the severity is Error and exit, the save is blocked and an error is displayed.