Secure Connect for Harness Cloud
Currently, Secure Connect for Harness Cloud is behind the feature flag CI_SECURE_TUNNEL. Contact Harness Support to enable the feature.
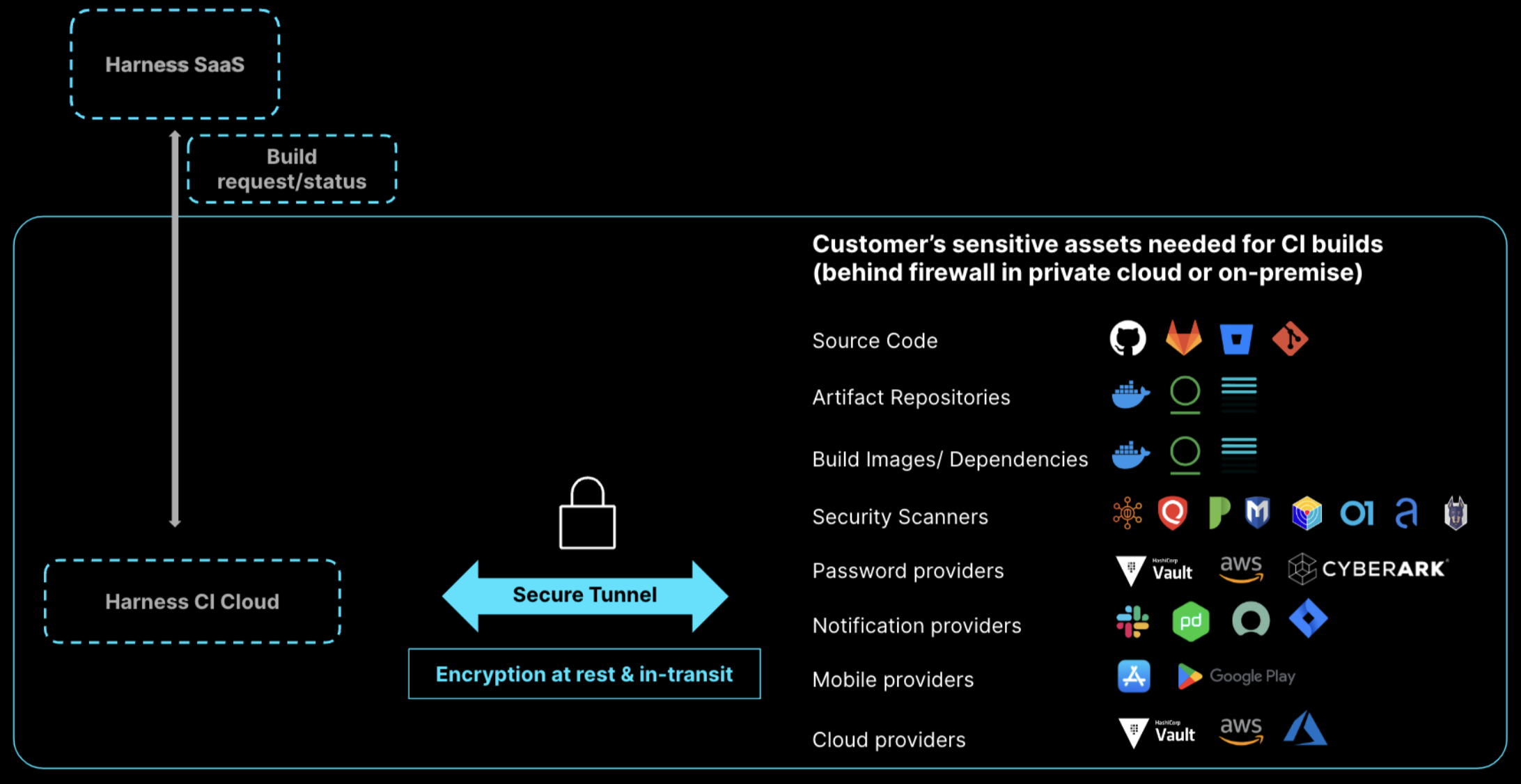
Harness CI Cloud (Harness-managed build infrastructure) addresses common challenges you might face when implementing a continuous integration tool in your infrastructure:
- Can I trust Harness CI Cloud with my intellectual property (source code, artifacts, and so on)? Yes. Harness CI Cloud doesn't retain your data after running a build.
- Can Harness CI Cloud securely connect to my complex and private firewalled infrastructure? Yes. You can use Secure Connect for Harness CI Cloud to connect to your private assets through a secure tunnel.
- Can I prove that Harness CI Cloud is secure so I can get it approved quickly by the required stakeholders (security team, ARB, DevOps platform team, infrastructure teams, and so on)? Yes. Harness CI Cloud has been penetration tested by external experts, and it is ISO and SOC2 certified. If you're already using Harness CI Cloud, additional approval isn't needed to enable Secure Connect to connect to your firewalled assets.
What is Secure Connect for Harness Cloud
With Secure Connect for Harness CI Cloud, you can connect to your sensitive assets through a secure tunnel. This allows you to use Harness Cloud build infrastructure with privately-hosted assets, such as internal artifacts repositories and on-premises code repositories. Secure Connect is a faster alternative to allowlisting IPs.
You can configure Secure Connect in minutes. If you're already using Harness Cloud build infrastructure, you don't need additional approval to enable Secure Connect.
| Secure | Effective |
|---|---|
|
|
Configure Secure Connect
-
Create a Harness API key with at least
RBAC:core_pipeline_viewandABAC:Allpermissions. -
Use the following command to run the Docker client in your firewalled environment. Where you run the client depends on what assets need to securely connect to Harness and your environment's network configuration.
docker run -it -e REMOTE_PORT=ANY_PORT_FROM_30000_TO_30100 -e REMOTE_SERVER=sc.harness.io -e API_KEY=YOUR_HARNESS_API_KEY harness/frpc-signedREMOTE_PORTis any port from 30000 to 30100.API_KEYis a valid Harness API key.
-
Enable Secure Connect for each connector you use with Harness Cloud that needs to route through a secure tunnel. This setting is available in each connector's Connect to Provider settings.
For example, if you need to connect to an on-premise code repo, you need to enable Secure Connect in your code repo connector's settings.
Compatible connectors include:
Use Secure Connect environment variables to route other clients
When you enable Secure Connect, Harness sets two environment variables: HARNESS_HTTP_PROXY and HARNESS_HTTPS_PROXY.
You can use these environment variables in cURL commands to tunnel other clients through the established secure tunnel, for example:
curl -x HARNESS_HTTPS_PROXY YOUR_ENDPOINT_URL
Replace YOUR_ENDPOINT_URL with the URL that you want to route through the secure tunnel. For example, you could route a private Bitbucket domain like https://bitbucket.myorg.com/.
The client must support connection by proxy.